Non-employees are becoming an increasingly essential part of today’s business workforces. High skill resources are harder to find, hire, and retain. Companies look outside of their own organization to find the skills they need to complete projects and business objectives. Managing the Non-Employee Workforce is as crucial as overseeing the internal workforce. For various reasons, both […]
A new way to think about IGA application connectivity and how to tackle the last mile. The last mile is a term used to describe the last stretch of road between the provider of services and the customer. This is the most difficult because there are a myriad of unknown obstacles and difficulties that exist […]
Using SCIM allows users to access resources within unrelated partner environments automatically without organizations needing to create and maintain external user accounts. What is SCIM and Why is it Important? SCIM or System for Cross-domain Identity Management is an open standard designed to secure and manage user identity data. Developed in 2011, the goal of […]
IDMWORKS Launches Lifecycle Auto Fulfillment to Enable Auto Access Provisioning to Every Application February 3, 2022 Miami, FL — IDMWORKS, consistently referenced by Gartner and Forrester as a top Identity and Access Management consultancy, today announced a unique solution that finally delivers automated, rapid access provisioning for the multitude of applications that are not currently […]
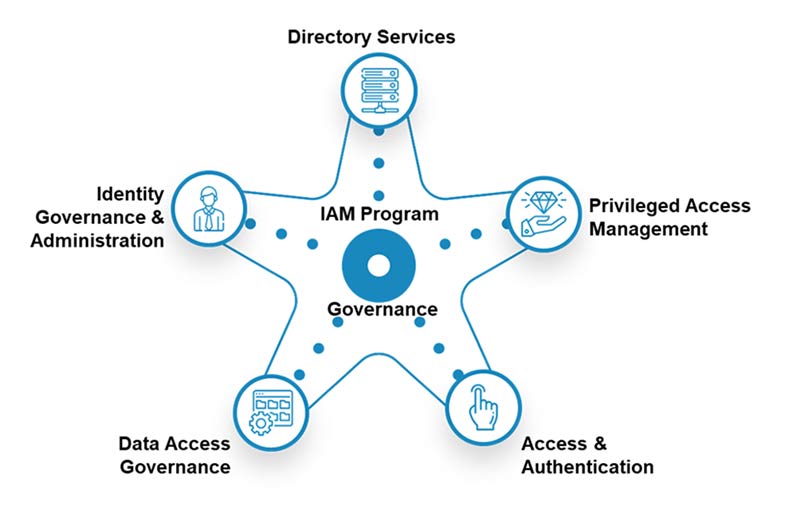
What Is an IAM Assessment Blueprint Roadmap? Why It Should Be a Top Identity Strategy for CISOs ? Part Three Data management continues to challenge businesses. Identity & Access Management is a powerful tool used by organizations around the globe to automate the process of tracking and assigning user privileges. A proper IAM Assessment or […]
Part Two: IAM Assessment Blueprint Roadmap Your organization is aware that it needs Identity & Access Management. You realize the value of IAM Assessments and how they can help you identify and address the challenges your organization faces when properly implementing an IAM solution. However, the question may still remain, what should you do with […]
IAM Roadmap from Assessment to Blueprint and then Roadmap (ABR) is the path to a digital transformation for all CiSCO’s. Your organization cannot afford to assume that its IAM solution in its current state is providing the protection you need. IT departments and business leaders are facing increased scrutiny on how they protect access to […]
How does a mature IAM program help limit the severity and scope of a hack? Like everyone else, I’ve been flooded with information about recent security events. There’s plenty of fluff circulating, but there is also some very good, thought-provoking discussions taking place. I recently read an article that discussed the idea of a “hack […]
Recently, we had a client run into an issue where certain users were being assigned roles, but entitlements were not being assigned according to the access policies. In this case, the roles, access policies, and scheduled jobs were configured properly, and there were no errors appearing in the logs. The access policies were not being […]
Harold Leavitt coined the phrase people, process, and technology in his 1964 paper, Applied Organization Changes in Industry. It’s been over a half a century since the introduction of this concept as a method to identify the key components for business success, yet IAM organizations (actually almost any organization) tend to default to solving problems […]